TRUSTED BY INDUSTRY LEADERS
Industrial and critical systems were never designed to be connected. Yet 70% of these systems* are connected today, making OT cybersecurity a critical priority in the face of escalating cyber threats.
Attacks are skyrocketing, security maturity is advancing slowly, and IT-first protection solutions create friction: massive false positives, operational disruptions, and misaligned language. Meanwhile, evolving cyber regulations are redefining the rules.
OT deserves protection that understands its constraints. Progressive. Non-disruptive. Immutable.
* Telstra/Omdia – 2025
USE CASES
SECLAB : Because we’ve all have something vital to preserve !
For over a decade, SECLAB has delivered security to the heart of the world’s most critical organizations, nuclear energy, defense, rail, and space.
We’ve pioneered enterprise-grade security solutions specifically engineered to meet the unique operational demands of companies relying on critical infrastructure.
The products of the Xcore platform

Seclab Xplore – See-First Intelligence
Learn more on Seclab Xplore

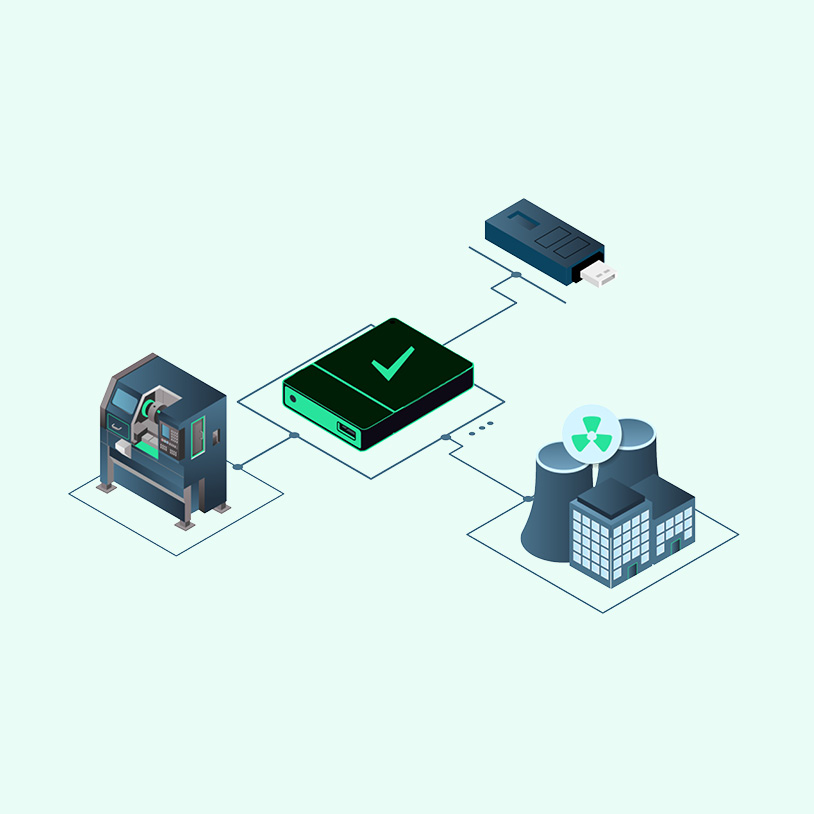
Seclab Xchange — Set-and-Forget Security
Seclab Xchange physically isolates critical OT assets from the rest of the network using patented Electronic AirGap technology. Seclab Xchange requires no maintenance operations or updates to maintain its security level.
Learn more on Seclab Xchange

Seclab Xport — Plug-and-Protect Technology
In OT environments, many assets are maintained via USB media, a common infection vector. Seclab Xport filters each file transfer before it reaches the target system. Simply plug it in, and the USB port is protected against physical attacks.
Learn more on Seclab Xport
Frequently Asked Questions