Digitalization of Practices & Opening to competition: IT Network and Signaling Network Separation
Context and requirements
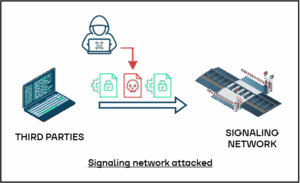
Following market liberalization, the railway company must allow third-party operators to access certain information (train positions within a station, trainset location, etc.), while ensuring a high level of security, as third parties must not be able to access the signaling network.
Requirements:
- IT / OT Interconnection
- Regulatory compliance
- Isolation of interconnection with third parties
Process
The company needed to compare several technologies (firewall, diode, protocol break application/hardware). Two findings were made:
- An attacker can exploit a vulnerability in security software that is not up to date.
- The use of a data diode forces the network into unidirectional transfers in a context where bidirectional communication is required.
A validation of the security level using the NATO test kit, as well as a functional validation of the architecture (application flows), were required.
Selected solution
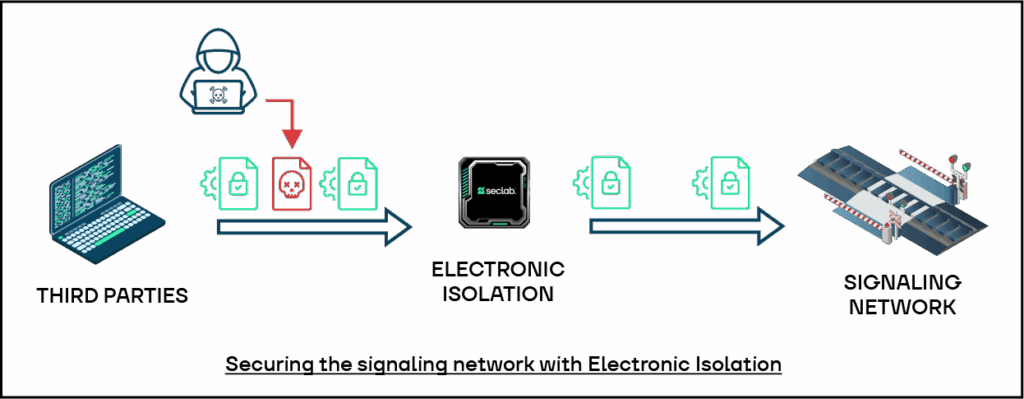
Selected solution was Seclab protocol breaking (in addition to Stormshield’s application-level analysis). This new architecture enables the company and the third party to exchange data in a bidirectional, secure, and controlled manner, thanks to protocol break enforced by electronics and filtering configured in accordance with the company’s security policies.
Results and customer benefits
Thanks to this new architecture, data exchanges are secure and controlled: information can flow between the company and the third party, but only files that comply with the company’s security policy are allowed to enter the network. Electronic isolation physically isolates and conceals the two environments.
Compliance: The architecture was certified compliant with the National Cybersecurity Agency of France requirements (ZEHO regulatory compliance).
Risk Management: The solution addresses the following risks:
- Footprinting / scanning
- Sophisticated network attacks
- Application-layer attacks
- Zero-day exploitation: no dependency on software patching
Long-Term Support: The solution provides a stable, sustainable, and maintainable architecture over the long term, independent of rapid software evolution cycles. It therefore ensures a lasting level of security and resilience.