Electronic Isolation: Understand how the technology that secures the most critical environments works.
A Technology Born from Operational Necessity
Traditionally, the most secure environments employed physical air gaps: completely disconnected networks with no digital communication pathways between systems. While highly secure, this approach creates significant operational challenges, and the strict physical air gap approach has become increasingly impractical.
Electronic Isolation technology emerged from a critical need expressed by industrial customers: How to achieve the security of physical network isolation while maintaining the operational functionality of bidirectional communications?
Developed and refined over a decade of deployment in the most demanding environments, this patented technology represents a fundamental breakthrough in network security.
This article explains how electronic isolation works.
The advantages of a safe-by-design technology
Electronic Isolation technology delivers true network segregation through a revolutionary approach:
- Complete Protocol Breaking: Electronic Isolation completely strips away and reconstructs network protocols (OSI layers 1-4)
- Payload Preservation: While network layers are destroyed and rebuilt, the application data (layers 5-7) remains intact, enabling full functionality
- Hardware-Enforced Security: This process occurs at the hardware level through specialized electronic circuits rather than vulnerable software components
This approach effectively creates an “electronic air gap” between networks while still enabling controlled data exchange, delivering security comparable to physical isolation with the operational benefits of interconnection.
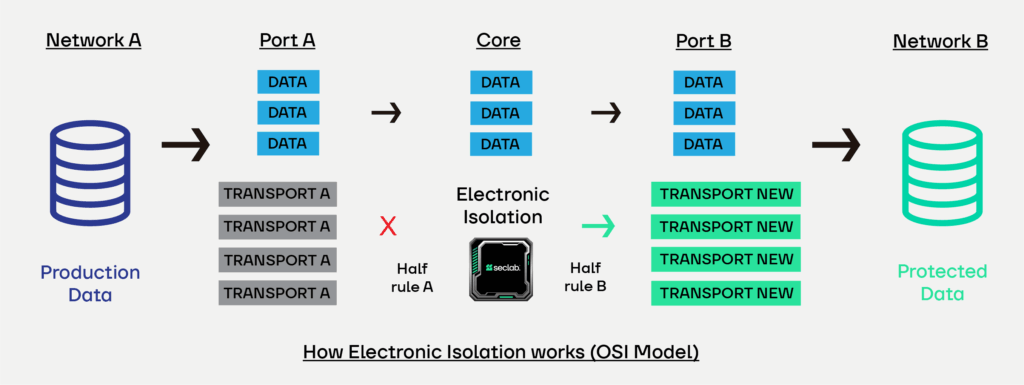
How Electronic Isolation works
The SecXN implements Electronic Isolation technology through a three-stage process:
Phase 1: Stripping Phase
Each IP packet from the source network has layers 1-4 completely removed, leaving only the application payload (layers 5-7).
Phase 2: Transmission Phase
The payload passes through a dedicated hardware channel to the output side, with no transport information
Phase 3: Reconstruction Phase
New, clean network layers 1-4 are generated and combined with the original payload before transmission to the destination network.
This patented process ensures that:
- No original network packets ever cross the boundary
- Transport-layer attacks cannot penetrate the protected network
- Network reconnaissance becomes impossible
- OS IP stacks, drivers, and network firmware remain protected
- Applications function normally without modification
Secure bidirectional communications
Electronic Isolation technology supports true bidirectional communications without compromising security:
- Full TCP/IP Support: Enables bidirectional TCP/IP communications without protocol-specific customization
- Encrypted Protocol Compatibility: Works seamlessly with VPN, SSH, HTTPS, and other encrypted protocols
- Native Application Support: Requires no application modifications or special proxies
- Direction Control: Allows administrators to control which side can initiate specific types of connections
In conclusion, Electronic Isolation now represents a major advancement in the protection of industrial environments, providing reliable hardware-level separation while preserving the communication necessary for operations. By eliminating the risks associated with traditional network connections, it enhances resilience against increasingly sophisticated threats. In a context where OT attacks are on the rise, this approach has become an essential building block for safeguarding critical infrastructures.
To learn more about this topic and gain a comprehensive comparative analysis with traditional cybersecurity solutions, we invite you to read our white paper, “Resilience and Control through Network Isolation”. To receive it, please fill out the form by clicking here.