Field Maintenance Operations Security
Context and requirements
In industrial environments, technical teams are regularly required to perform interventions on critical assets, some of which operate on legacy operating systems that organizations must maintain in service for several decades. Connecting these assets to the network is often impossible or represents an unacceptable risk. To ensure proper operational continuity, teams frequently rely on USB drives to deploy firmware updates, apply new configurations, or perform diagnostic operations.
These interventions, sometimes executed under time pressure, can introduce compromised USB devices that threaten the integrity of critical systems. USB drives thus represent a significant attack vector (malware, ransomware, targeted attacks).
The organizational requirement was therefore to secure field maintenance operations on obsolete legacy equipment through strict isolation between USB peripherals and these critical systems.
Implemented solution
The organization adopted Seclab’s hardware protocol break-through solution, a USB isolation device that enabled secure data transfer with enforced restrictions via a physical relay. Xport is an external appliance that connects directly to the USB port requiring protection and requires no installation or modification to the protected equipment. It isolates the USB port, blocks attacks inherent to the physical medium, and filters all data transfers destined for the critical system.
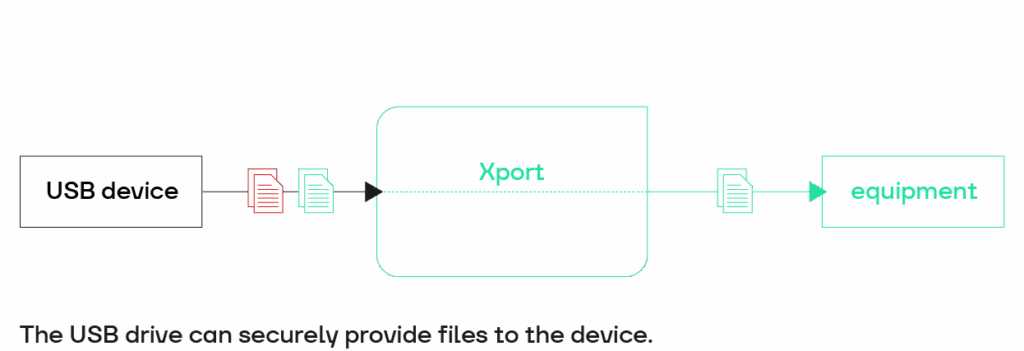
Xport provides directional control of exchanges: unidirectional or bidirectional. Through this appliance, the organization gained a security gateway to validate authorized data transfers during maintenance operations.
The organization also implemented a digital signature process for authorized files deployed to critical systems, as close as possible to the source system (e.g., PLC firmware). Through this digital signature verification, Xport ensures that no unauthorized modifications or additions to files occur prior to authorizing transfer.
Results and benefits
Enhanced Security Posture: Through USB isolation, the organization strengthened the robustness of its infrastructure and the operational safety of its installations. The organization continues operating legacy systems, which cannot be replaced, without compromising cybersecurity.
Improved Operational Efficiency: Operations previously prohibited due to excessive risk are now viable. Post-incident operational forensics and diagnostics are enriched through the secure export of logs and local files via USB.
Standards Compliance: The electronic isolation enables compliance with critical industrial cybersecurity standards: NERC CIP, ISA/IEC 62443, NIST 800-53, and NIST 800-82.