Increase Safety and Security of Gaz Leak Detection Process at PG&E .
Introduction and context:
PG&E, The Pacific Gas and Electric Company, is an American provider of natural gas and electricity to 5.2 million households in the United States.
Focus on gas distribution:
- 8 compressor stations
- 40,000 milesof distribution pipelines
- 6,000+ miles of transportation pipelines
- 2 million customers
In 2010, San Bruno California suffered a blast in the heart of the city. With major damage and people’s casualties, accidents revealed that gas pipeline defects were involved. PG&E was also accused of not being able to fully control the whole pipeline infrastructure, though not being able to detect gas leak for example.
Architecture evolution:
At first, gas leak detection sensor infrastructure lied on a simple architecture, each of these sending their data to a secured centralized control room.
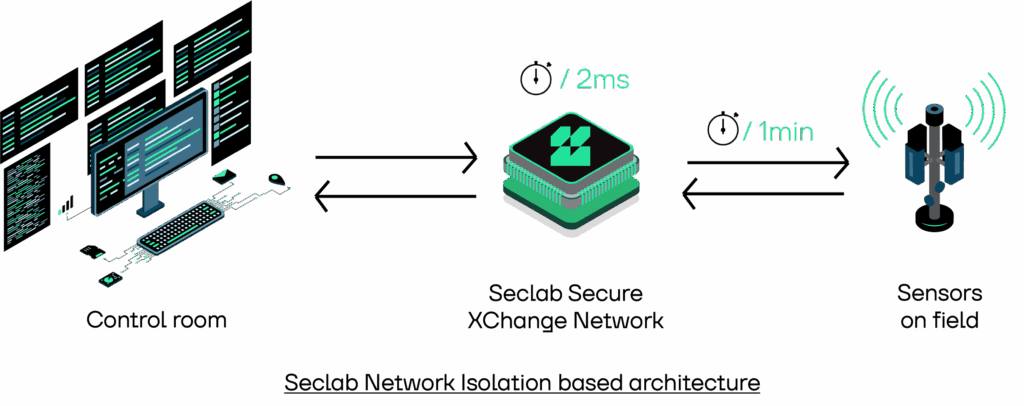
With increased cyber security risks and to prevent external network access to its control room, PG&E decided to upgrade its architecture:
- Changing physicalsensors hardware and control room software for modern ones.
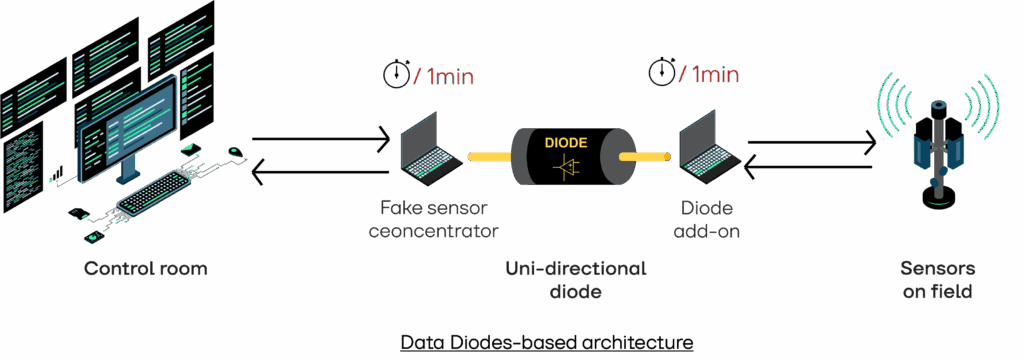
- Implementing a complex network data diode architecture to support new hardware.
Pain points / New architecture results:
Network Diode based architecture is ok with limiting the network flow direction. As stated by regulators, this is not an isolation of the control room network from fields’ sensors network, but it is acceptable from a cyber security perspective.
Communications between control room and field sensors are bi-directional by design, but diodes are mono directional.
Network Data Diode based architecture leverages segmentation of Network Diode based architecture and allows simulation of bi-directional communication, but it introduces latency on communications. The time to detect was more than 2 minutes. Also acceptable from a Cyber Security perspective, Safety penalty is too much to handle because of latency.
This is why PG&E led studies on an architecture that offers at least the same cyber security level but reduces the time to detect.
Expectations:
Needs are to:
- Have true isolation, not only segmentation between field network and control room
- Keep the time to detect delay as short as possible (2 minutes is too long)
SECLAB proposal:
Compliance: With its appliance, SECLAB offers a way to allow bi-directional controlled communications between true segregated networks.
Safety: Electronic Airgap driven hardware offers a shortened latency over data diode architecture (2 to 4 milliseconds latency against 1 minute or more).
Cybersecurity: Designed first for highly critical systems and defense networks, the appliance is secure by design.
Results and new expectations:
PG&E decided to evaluate the intrinsic security of the appliance, leading penetration tests comparing the appliance with a firewall. Those tests confirmed that the level of security provided by the appliance was the best in the context.
After evaluation of the proposed architecture, PG&E Head of Digital Transformation Team argued that it changed responsibilities repartition. Fact that bi-directional communications were now possible from the control room to the sensor, one could not only ask metrics and information from sensors but also command and control these sensors. This new paradigm was not acceptable. Hopefully, the network protocol used to communicate was Modbus and clearly identify read only operations from write operations. SECLAB proposed to apply a filter that only allows “read” operations to go through. This solved the problem.
It took a short time to make the appliance online and fully functional with very minimum impact.