OT Network Mapping and Intelligent Detection
Map your industrial assets comprehensively, monitor your infrastructure, and detect attacks in real time using non-intrusive discovery and artificial intelligence. From one-time audits to continuous monitoring, Seclab Xplore supports your cyber maturity journey without ever disrupting operations.
Are these challenges familiar to you?
To address these issues, choose an OT-designed visibility and detection solution that provides the most comprehensive mapping available on the market.
SEE WITHOUT DISRUPTION: A CHALLENGE IN OT
In the OT world, each newly deployed security device brings its own set of constraints:
- Risk of impacting the availability of critical processes
- Deployment and maintenance complexity
- Massive generation of false positives
- Contractual limitations on certain OT systems
Traditional visibility and detection solutions face significant limitations in this regard.
>> Traditional solution = installation of intrusive software components on operational equipment.
>> Traditional solution =
IT-oriented operation mode, difficult for industrial teams to understand, generating noise and potentially disrupting operations.
For Visibility that Truly Respects OT Specificities
Seclab offers a non-intrusive discovery and intelligent detection approach with Seclab Xplore, the only sovereign visibility solution for industrial environments.
Multi-View Mapping
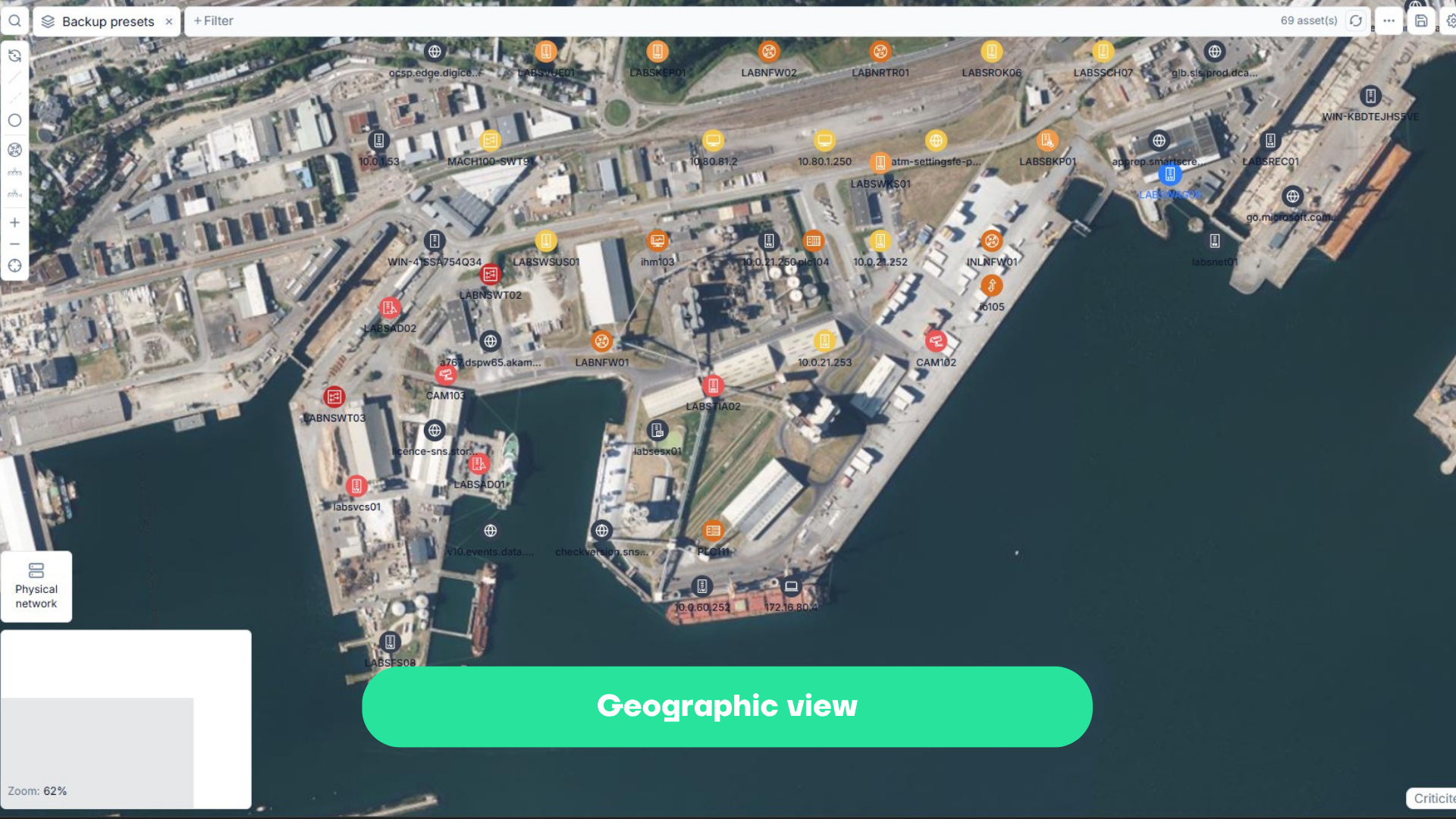
- Geographic view: spatial positioning of assets. For site managers and OT leaders.
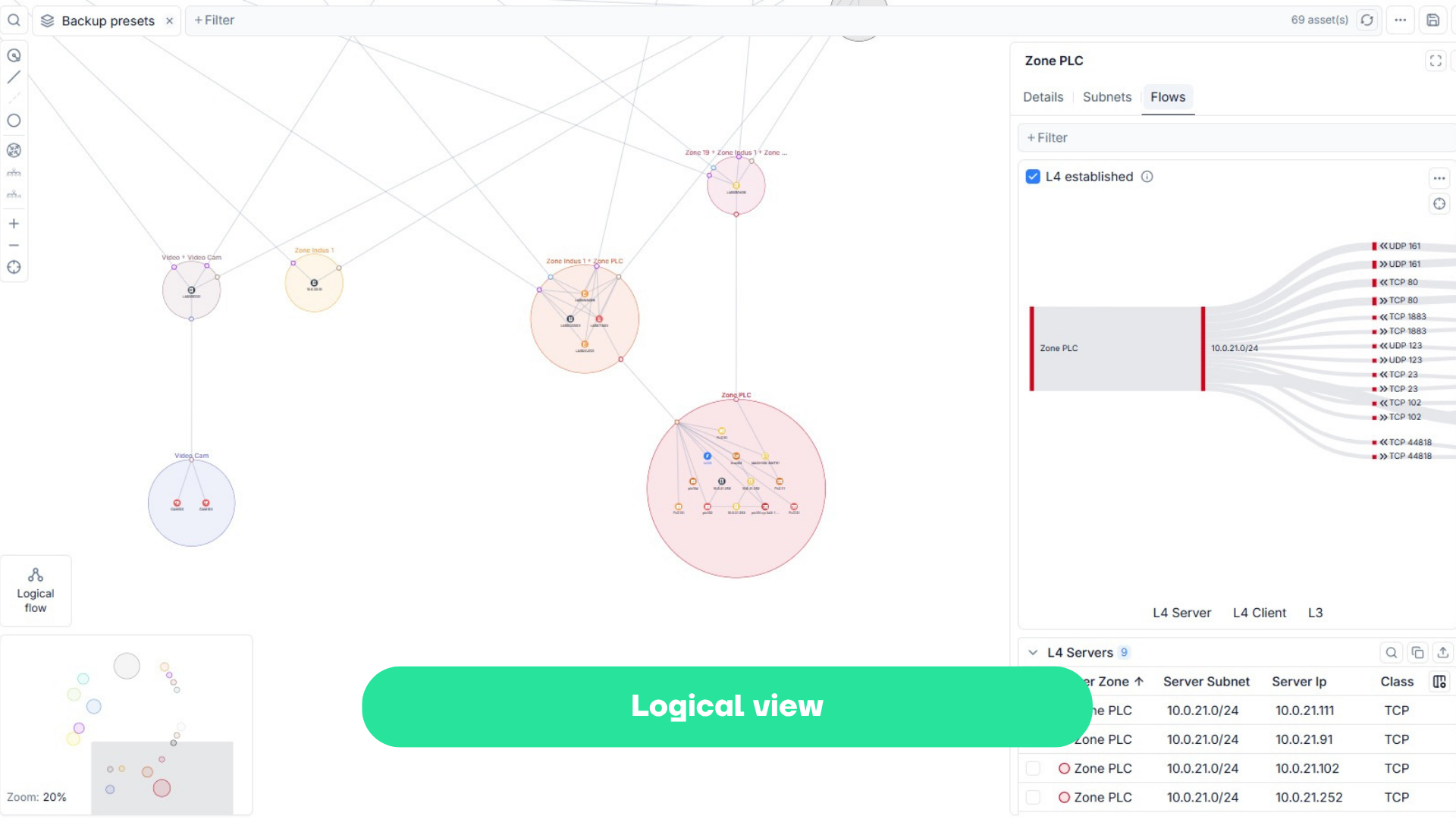
- Logical view: communication flows represented as zones and conduits. For CISOs and security teams.
- Business view: functional perimeters. For automation engineers and OT managers.
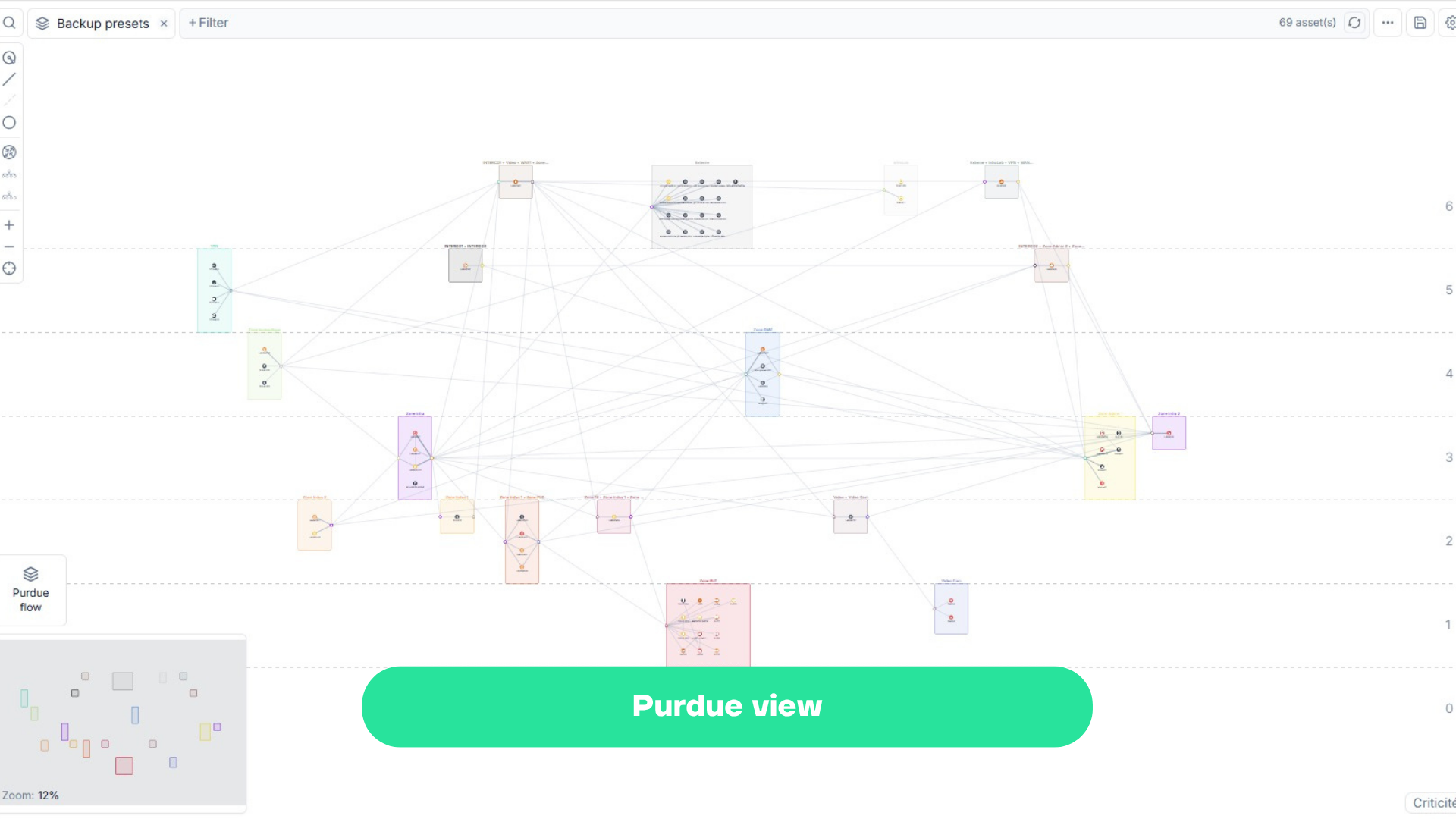
- Purdue view: organization according to the IEC 62443 model. For automation engineers and OT managers.
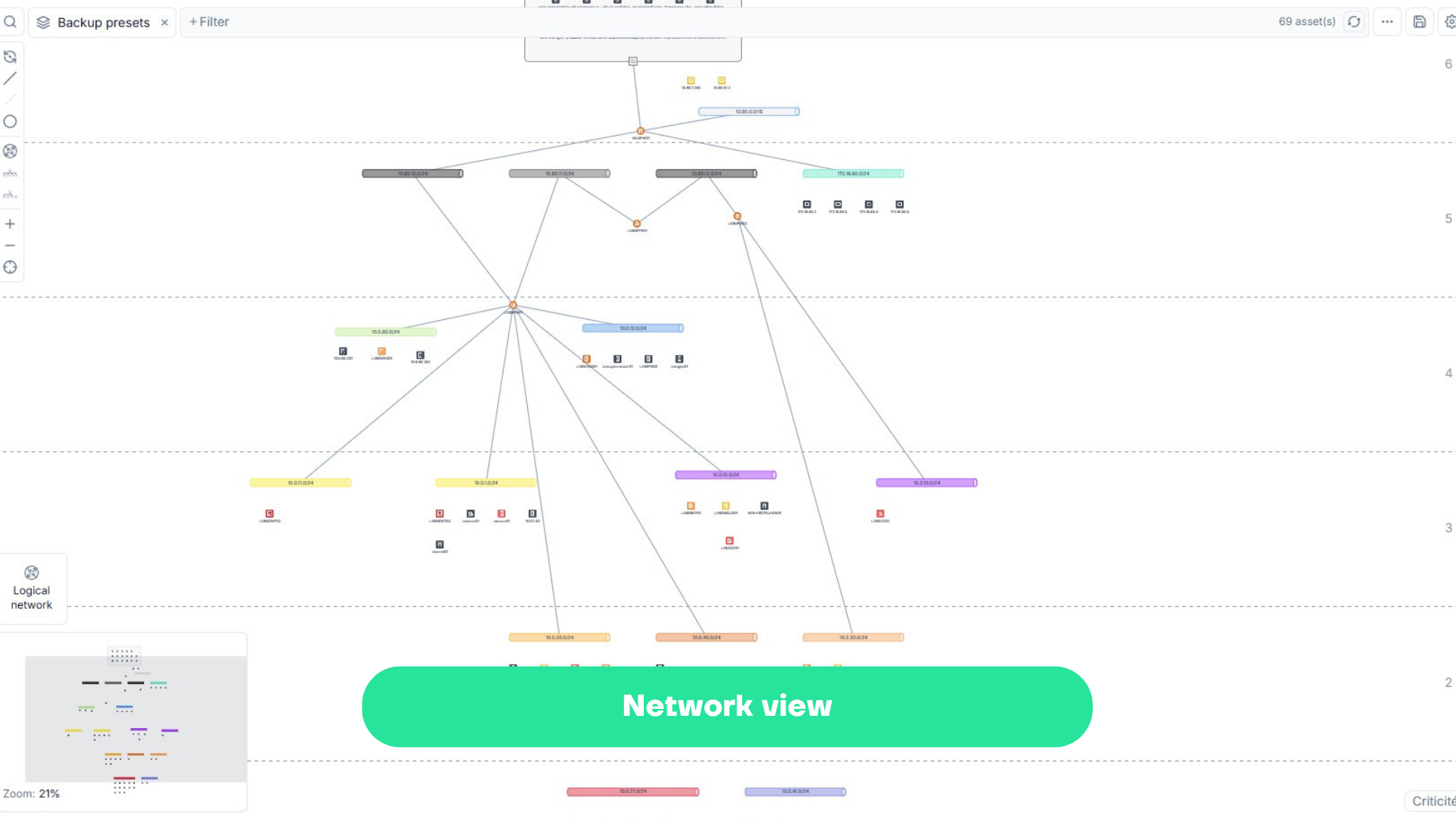
- Network view: classic network topology. For network engineers and system administrators.
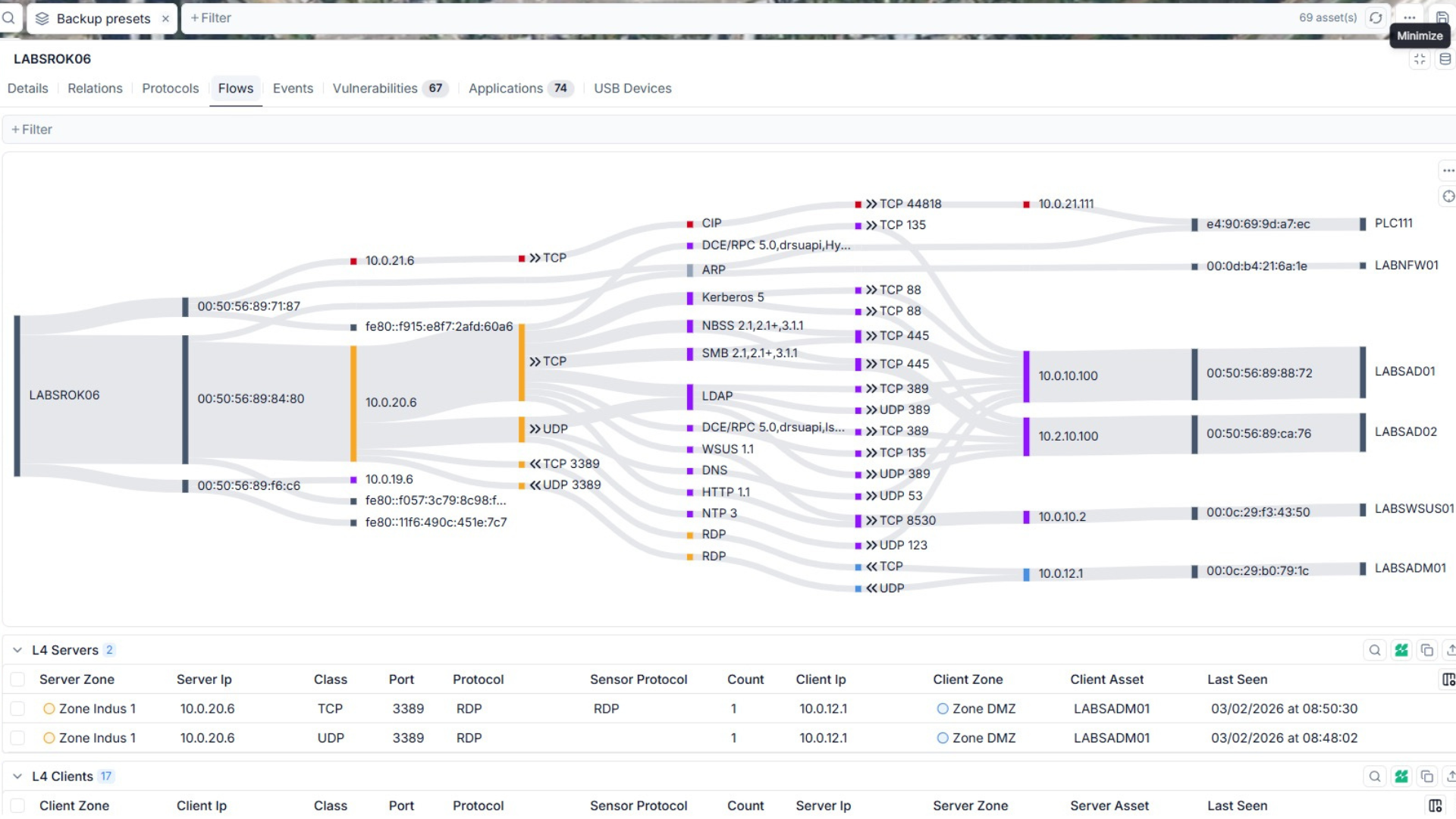
Flow Matrix
For each asset, zone, or link, displays a representation of communications with other connected devices.
- Communicating assets
- Protocols used
- Direction of communications
- Network zones
Seclab Xplore natively inspects industrial protocols (Modbus TCP/RTU, S7comm, EtherNet/IP, OPC-DA, BACnet, DNP3, IEC 60870-5-104, PROFINET,etc.).
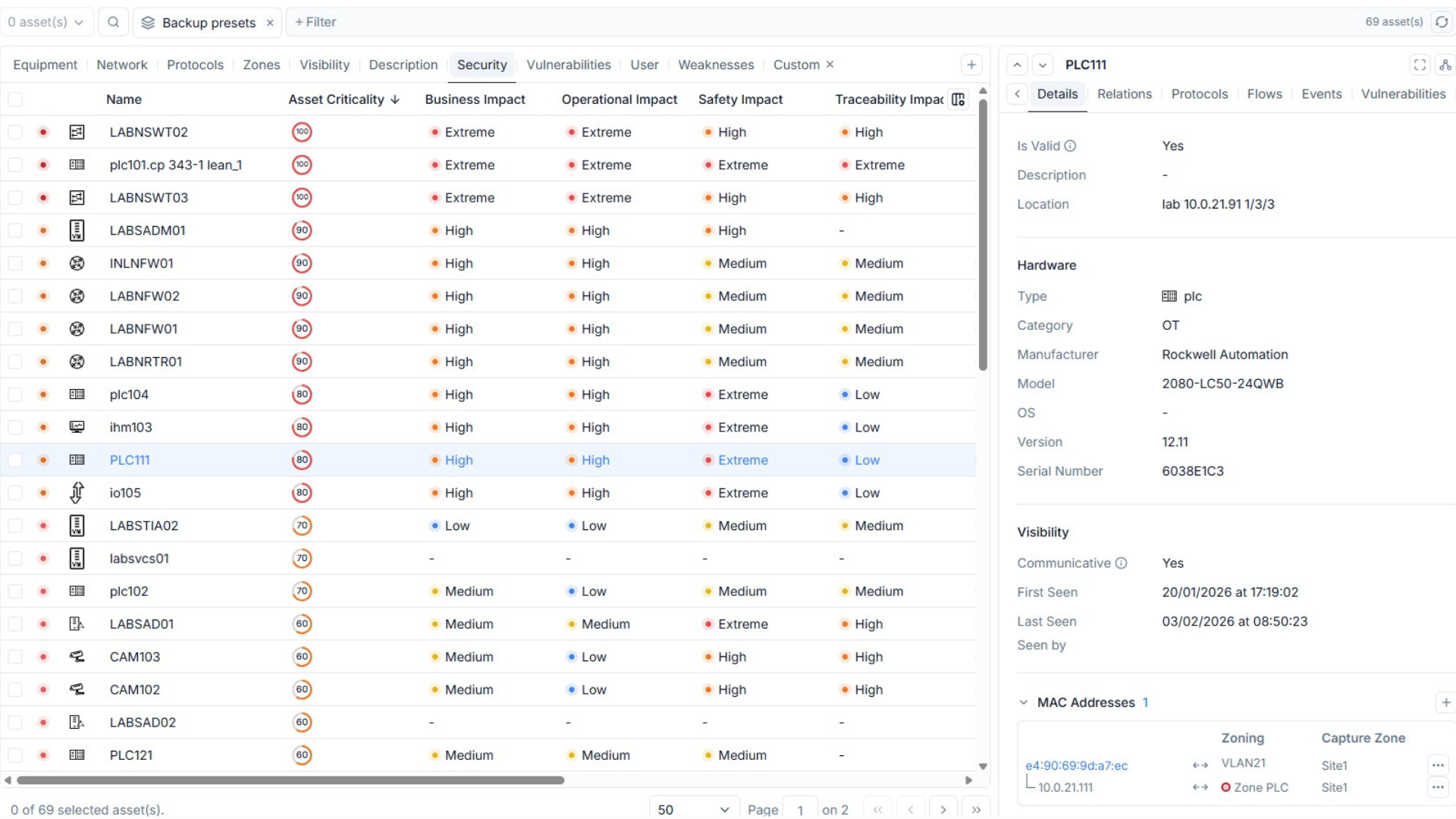
Risk-Oriented Inventory
- Hardware type
- Network equipment
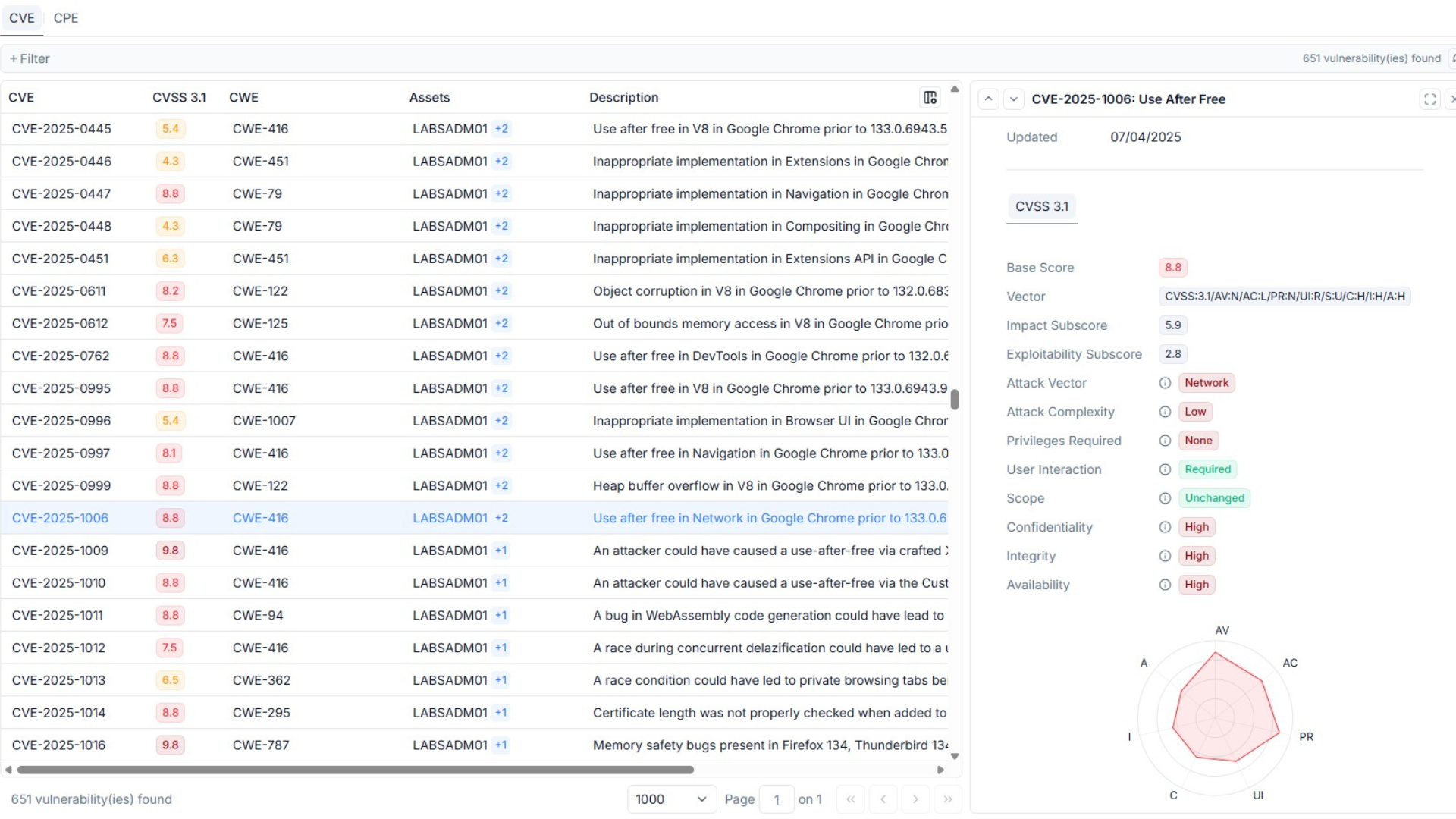
- Asset vulnerabilities
- Risk level assessment for each asset
Risk is evaluated according to the following criteria: business impact, operational impact, safety, traceability, availability, backup, confidentiality, integrity, and recovery priority.
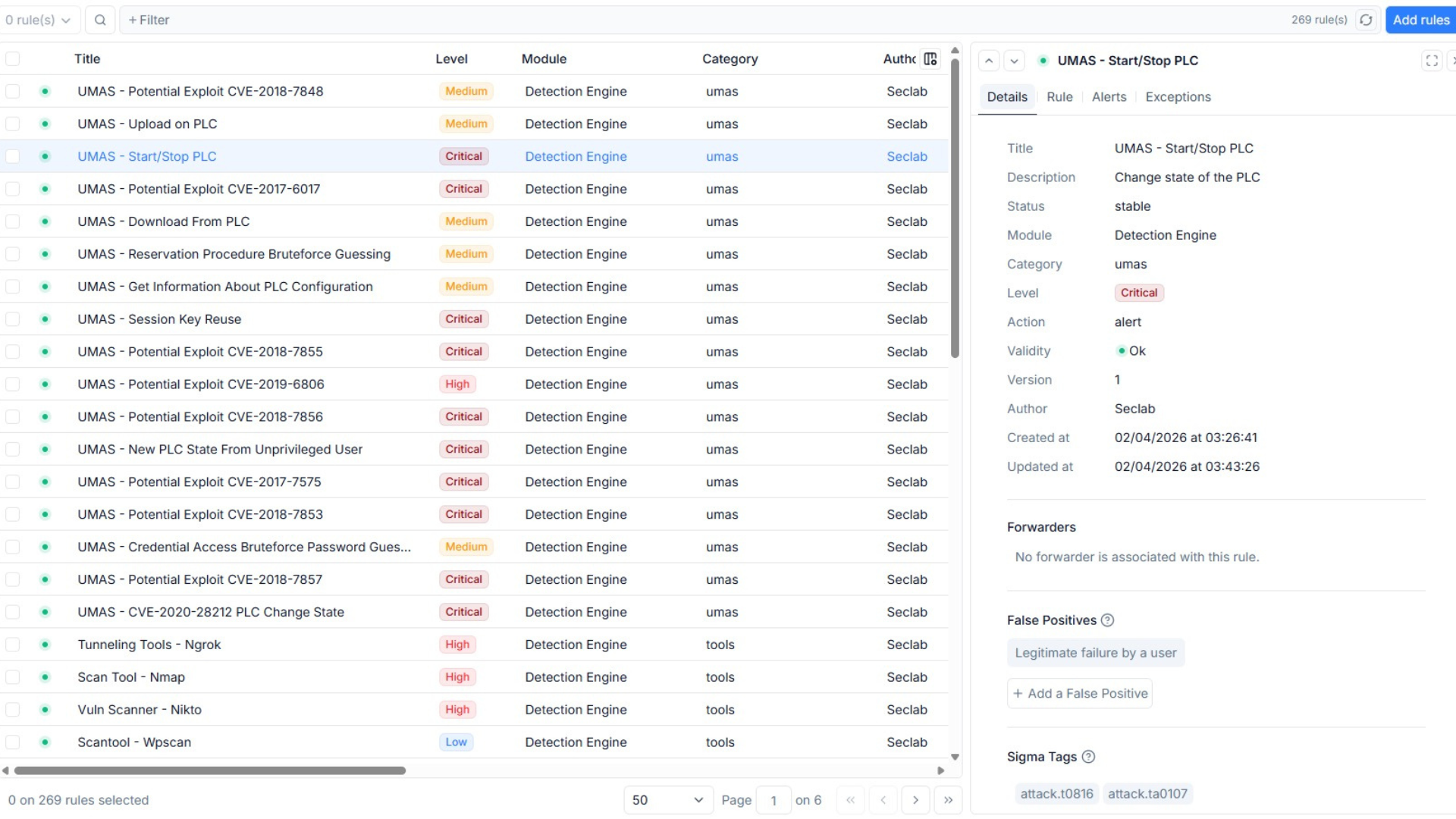
Intelligent and Contextual Detection
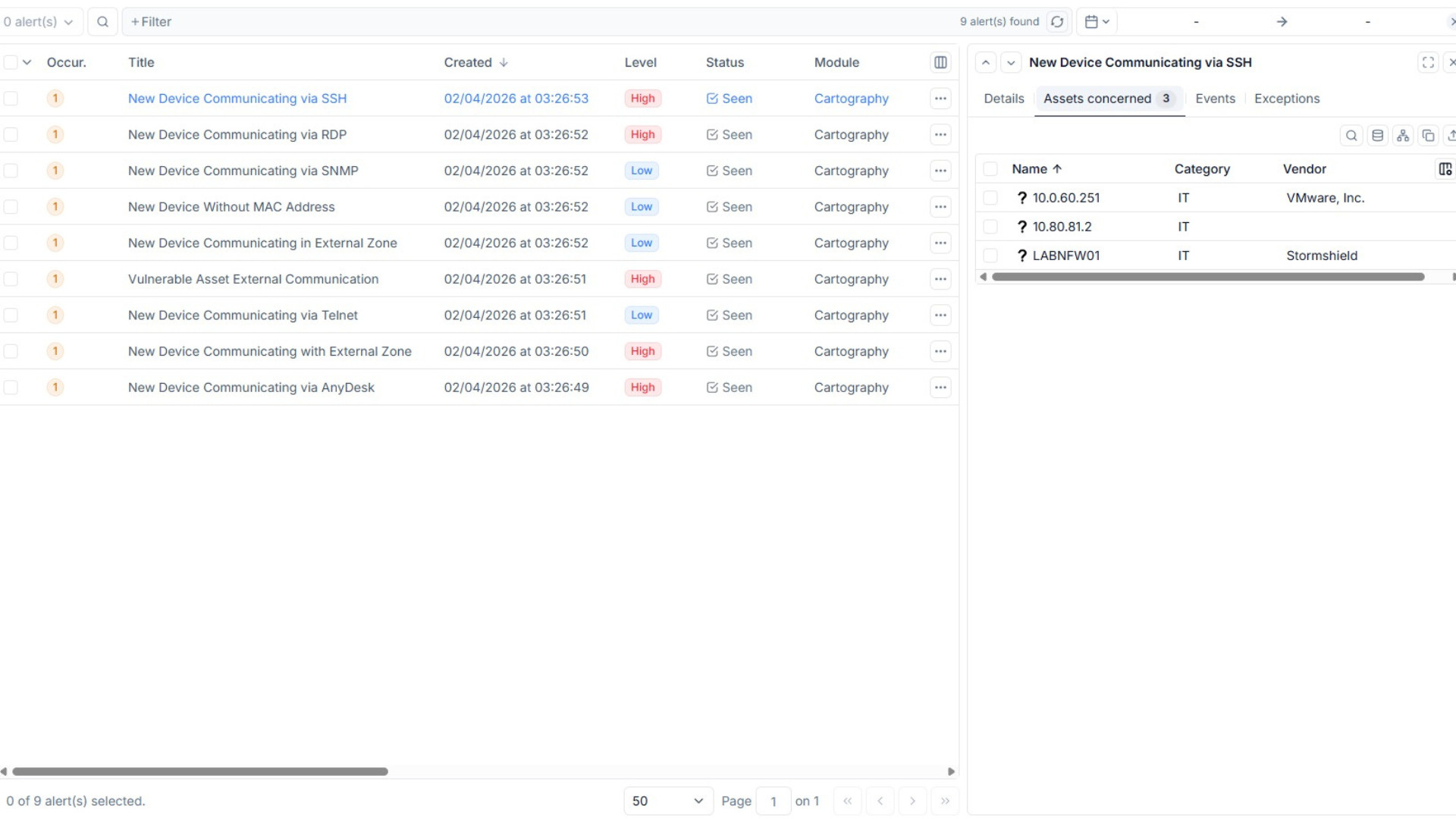
- Cartography-based detection: identifies new assets, ports, and network flows.
- Sigma signature detection: customizable and contextualized rules.
- Suricata signature detection: network-based instrusion detection.
- Behavioral detection powered by AI: learns normal patterns and identifies deviations.
Unmatched Visibility
Five mapping views generated automatically or manually from the same data. Capable of operating on core networks, non-routed networks, and isolated perimeters.
Intelligent Threat Detection
Four complementary engines (mapping, Sigma signatures, Suricata signatures, AI behavioral) to identify anomalies, zero-day threats, and weak signals. False positives are minimized thanks to mapping-based contextualization.

Progressive Path
From ad-hoc audits to continuous supervision, using the same software. Existing inventories can be enriched. Controlled initial investment, with scaling at your own pace.
Regulatory Compliance
Actionable data for NIS2 or IEC 62443 audit reports. MITRE ATT&CK coverage reporting. Auditable inventories, documented network maps, and complete flow matrices. Demonstrates clear control over risks.
Facilitated IT/OT Collaboration
Intelligent alert routing by recipient, collaborative mapping, and native interoperability with existing tools (firewalls, SIEM, SOC, bastions, CMDB). Each team works in its familiar operational view.
Trusted Solution
French solution developed and maintained in France, with full control over code, data, and roadmap. Complete sovereignty over your OT data.
Key OT Visibility Use Cases Leveraging the Unique Capabilities of Seclab Xplore
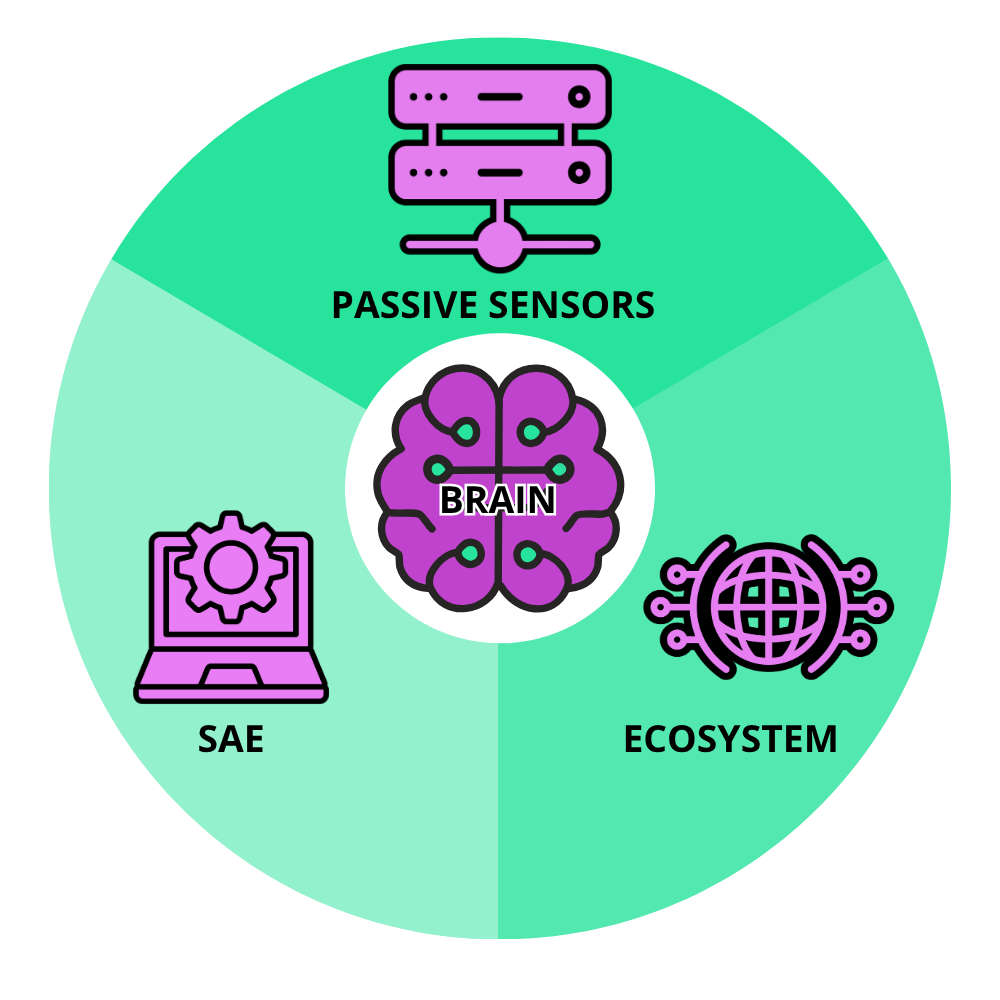
SECLAB XPLORE – HOW IT WORKS?
Seclab Xplore operates without scanners or agents to discover assets, routing or filtering equipment, and to map network flows—without ever disrupting industrial processes. Zero impact on operational availability. The solution includes the following components:
4
100%
Mapping Views
Detection Engines
Designed for OT
Your OT Environment Deserves Defense in Depth
> For physical network isolation and protection of critical assets, discover Seclab Xchange.
> For securing assets using USB devices, discover Seclab Xport.
> Xchange, Xport, and Xplore are part of the Seclab XCore Platform, providing lasting confidence in the cybersecurity of operational and industrial environments.
> Discover Seclab XCore Platform, the cybersecurity platform designed by OT, for OT.
Frequently Asked Questions