Seclab Xcore Platform,
for Defense in Depth in OT
The platform combines comprehensive visibility of OT assets, electronic isolation of critical perimeters, and continuous AI-enhanced attack detection.
Are these challenges familiar to you ?
To address them, adopt a progressive, step-by-step approach designed for the realities of OT and critical environments, with Seclab Xcore Platform.
OT CYBERSECURITY: THE ALL-OR-NOTHING TRAP
Most OT cybersecurity approaches impose a monolithic deployment:
• full solution purchase from the outset,
• probes deployed across the entire perimeter from day one,
• ongoing maintenance workload incompatible with OT team constraints.
This “all-or-nothing” model slows adoption, increases initial costs, and creates an operational burden that industrial teams cannot absorb.
Moreover, deploying protections without first having a clear understanding of what needs to be secured is a guaranteed failure.
>> IT solutions transposed to OT make the problem worse:
- intrusive components on fragile equipment,
- additional maintenance operations,
- massive false positives,
- IT-oriented alerts that lack a business-focused approach.
For True Defense in Depth that Genuinely Respects OT-Specific Constraints
This approach is based on two realities:
- Industrial organizations all have different levels of cyber maturity.
- Not all assets need to be protected at the same level.
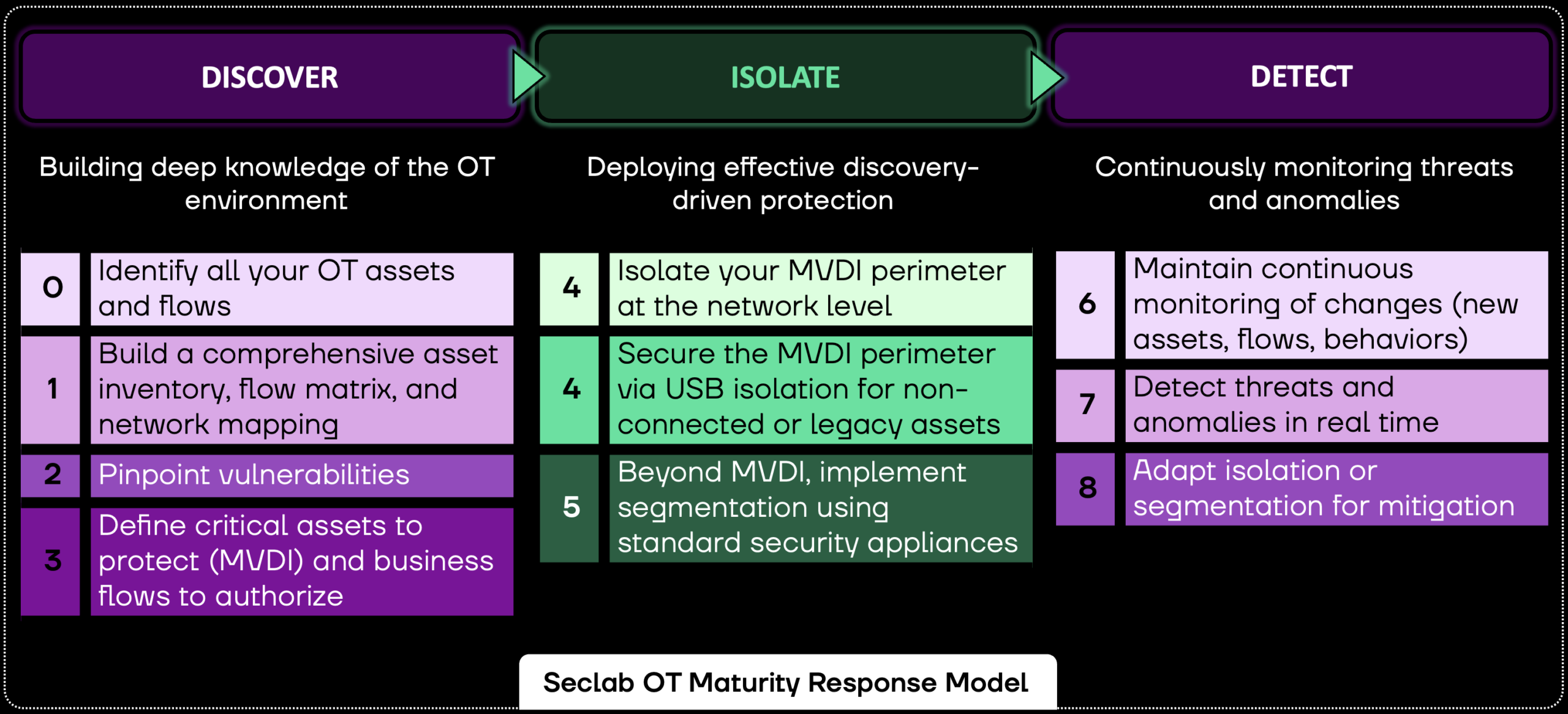
8 progressive milestones, structured into three phases.
Each phase (Discover, Isolate, Detect) lays the foundation for the next and corresponds to a software or hardware solution.
The approach incorporates the concept of MVDI (Minimum Viable Digital Industry), a perimeter that includes only the critical assets required for the continuity of business operations.
>> Discover to clearly identify critical assets connected to the network or using USB ports (MVDI).
>> Isolate to protect this MVDI with maximum security so that a security incident cannot bring down the business.
>> Detect to ensure continuous monitoring of the infrastructure, especially in non-isolated areas, thereby reducing analysis workload and false positives.
Even in the event of an attack, what matters most is preserved and everything can be restarted.

More than Detection
Deployment Success
Security at your Own Pace
Low Impact on Production

Regulatory Compliance
Technological Sovereignty
A French solution developed and maintained in France, with 100% European capital, full control over code, product manufacturing, data, and roadmap.
The Products of the Xcore Platform

Seclab Xplore – See-First Intelligence
Learn more on Seclab Xplore

Seclab Xchange — Set-and-Forget Security
Seclab Xchange physically isolates critical OT assets from the rest of the network using patented Electronic AirGap technology. Seclab Xchange requires no maintenance operations or updates to maintain its security level.
Learn more on Seclab Xchange

Seclab Xport — Plug-and-Protect Technology
In OT environments, many assets are maintained via USB media, a common infection vector. Seclab Xport filters each file transfer before it reaches the target system. Simply plug it in, and the USB port is protected against physical attacks.
Learn more on Seclab Xport
Frequently Asked Questions